How to give great employee performance reviews

En Dropbox Sign-blogg om
All articles
Sign contracts 80% faster
Go paperless with Dropbox Sign.
Prova Dropbox Sign
The foolproof guide to creating the perfect hiring sequence
Sätt ihop en enkel och smidig process som är lätt att följa och genomföra som gör den positiva kandidatupplevelsen till standarden.
Ladda ner

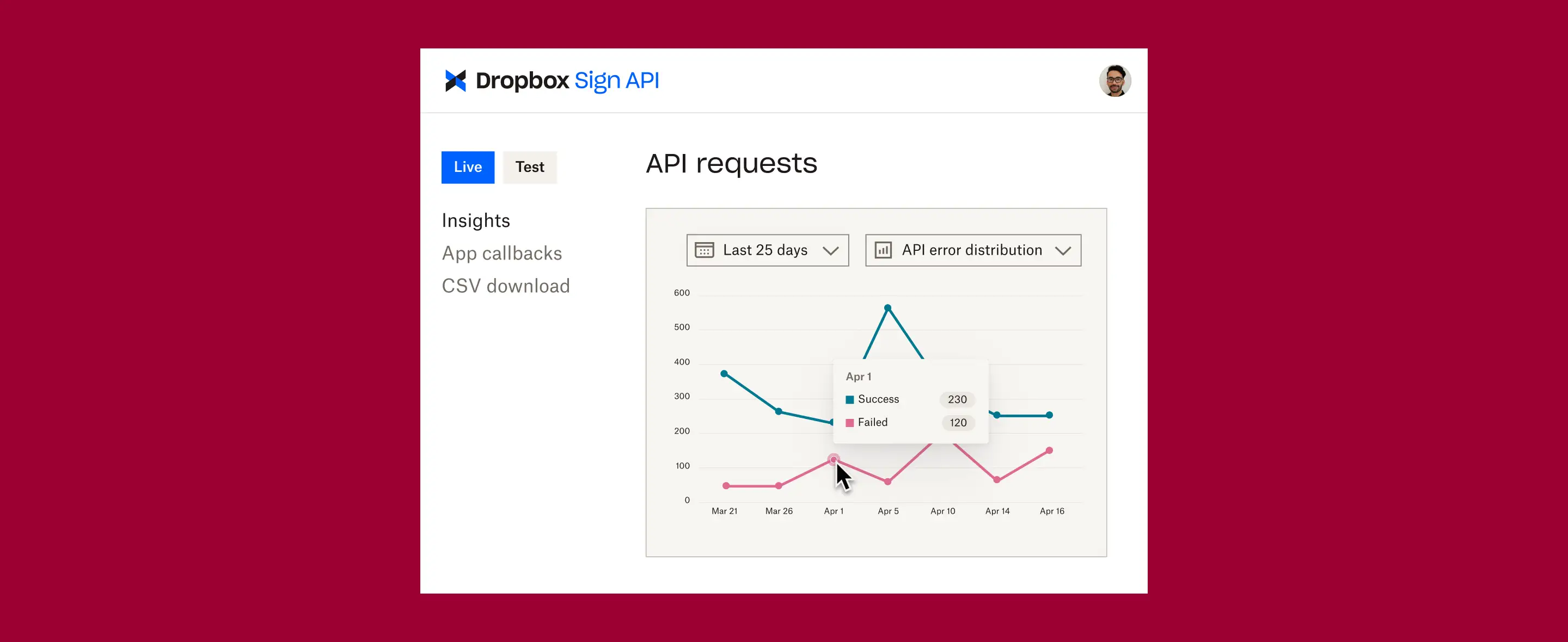
Dropbox Sign integrations
Ready to experience our new and improved Dropbox Sign for HubSpot integration?
We’re offering new Dropbox Sign users 50% off the first year!
Påbörja din kostnadsfria provperiod



































































![How To Boost Buyer's Confidence [Updated 2023] editorial illustration](https://assets-global.website-files.com/6446df33610093270e7fb677/645a79cf551d724a508f6ce3_6449bddbf539fc2c4cbafc7f_uc.webp)
![How To Boost Buyer's Confidence [Updated 2023] editorial illustration](https://assets-global.website-files.com/6446df33610093270e7fb677/645a79cf551d720f3c8f6ce4_6449bddbf539fc49dabafc81_uc.webp)






















.webp)